Blog
Organizations are placing a lot of emphasis on their security posture, or…
Data centers and server rooms are evolving, to be sure. Enterprises have…
Overview In order to regulate the hardware, software, networking, operating system (OS),…
Real-time IT infrastructure analytics provides actionable information. A solid IT infrastructure can…
An IT architecture known as a “public cloud” uses the public Internet…
According to Gartner, a “workload-centric security solution that tackles the particular protection requirements”…
By monitoring, detecting, and blocking unwanted privileged access to vital resources, privileged…
Data loss prevention (DLP) identifies and stops sensitive data breaches, exfiltration, and…
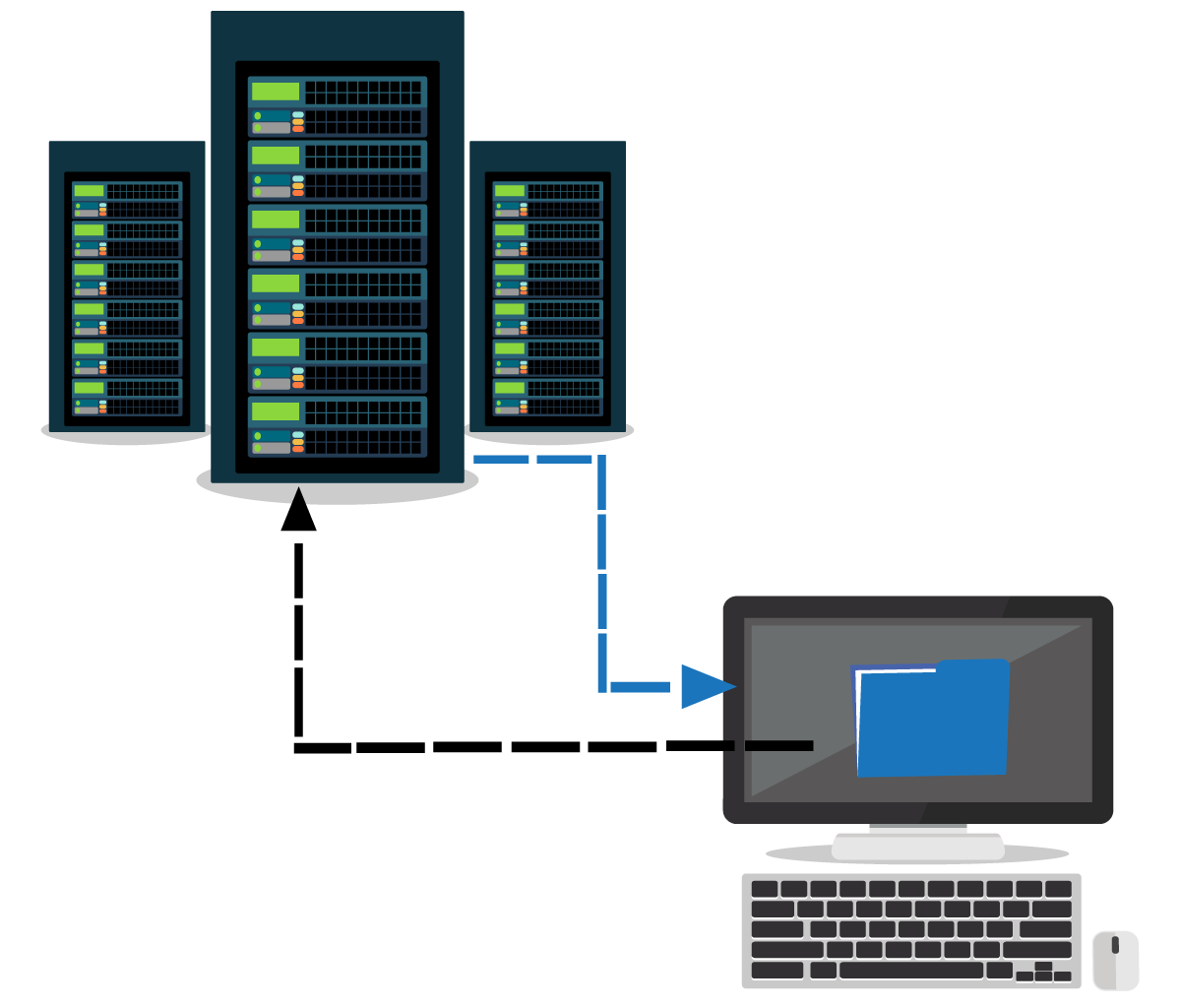
The term “virtualization” in the context of computing or cloud computing refers…